List of Features
100%
recovery rate
Step-by-step
file recovery wizard
Recovers files deleted
without Recycle Bin
Restores after
a virus attack
Restores from
corrupted partitions
Search files
based on content
Thumbnail
gallery
Any types
of file systems
Pre-recovery
preview
Data export
wizard
Simplicity
of use
Recovery of
compressed files
Working with
drive images
Built for
MS Windows
Show more
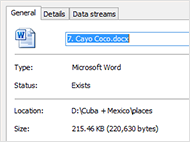
100% recovery rate with thorough integrity checks
Unlike competing tools, Magic Office Recovery validates every document it’s about to recover with a thorough integrity check.
This means that only those files that are actually 100% recoverable end up getting listed in the thumbnail gallery. This automated integrity check makes for uncluttered recovery experience. Instead of seeing remnants of hundreds of broken documents, you will only see a few – but those few are 100% recoverable, guaranteed.

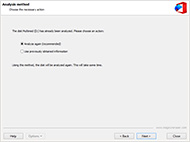
Step-by-step
file recovery wizard
A fully guided wizard is available to assist you with the recovery process, guiding you through the entire process to ensure safe recovery and smooth operation even if you have no prior experience using recovery tools.

Recovers files
deleted without Recycle Bin
Many programs at removal of a file from a disk do not use a Recycle Bin. Even considering, that these files are not present, you can find them on a disk and restore. Also you can restore files removed from a Recycle Bin.

Restores data
lost after a virus attack
Information can be lost for many reasons. Files could be removed, if your system was attacked by a virus. Some programs also can remove erroneously files. You can restore them, using Magic Office Recovery.
Recovers documents from corrupted and inaccessible media
Magic Office Recovery shares its data recovery engine with Magic’s top of the line tool. This highly sophisticated engine enables surefooted recovery even if the documents are located on a severely damaged, corrupted or unreadable disk. The engine features two recovery modes: Quick and Comprehensive. In Quick mode, the tool works blazing fast, and is able to recover recently deleted documents in just seconds. Comprehensive recovery works great for damaged, corrupted and formatted disks.

Content-aware analysis: search files based on content
Magic Office Recovery features a comprehensive data recovery engine borrowed from Magic’s top of the line tool. The engine employs our signature content-aware analysis algorithm allowing the tool to recover documents from badly damaged media.
Content-aware analysis works by accessing the disk in low level, reading every sector and scanning the data for certain patterns characteristic to documents in known formats. Once a pattern is detected, the engine performs an integrity check and adds valid files to the list of recoverable documents.
Thumbnail Gallery
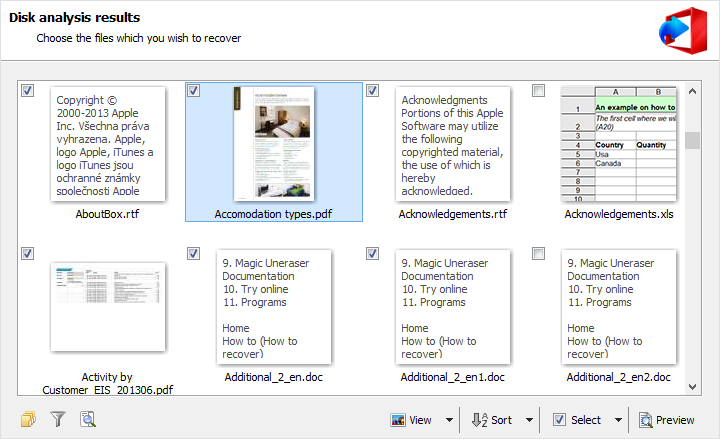
Thumbnail gallery signifies logical evolution of pre-recovery preview. Recoverable documents are displayed as thumbnail-sized images, making it easy to browse through the files and discover exactly the document that you were to recover. Thumbnail view allow easily navigating through multiple files. The available sorting and filtering options allow quickly displaying files matching specific criteria – like those that were last modified during the last day.
Any types of file systems
Recovers documents from disks formatted with FAT/FAT32, NTFS 4/5. Content-aware search thoroughly analyzes raw disks even if no file system is available.
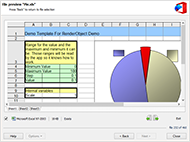
Preview before you recover
The built-in pre-recovery preview uses a fully independent viewer that does not require Microsoft Office or OpenOffice to be installed.

Data Export Wizard
Recovered files can now be saved not only to hard and removable disks, but burned to CDs and DVDs, and can also be uploaded to an FTP server.
Simplicity of use

With all the powerful features under the hood, Magic Office Recovery is designed to be used safely by non-pros. The tool offers an easy way of fixing common issues and repairing serious problems. Thanks to it the product is very simple in work and understandable for any user – both skilled, and for the beginner. A fully guided, step-by-step wizard will assist you in fixing all types of damage from recovering individual files to refurbishing broken partitions.
Recovery of compressed files
The NTFS file system allows compressing files to save disk space. The program can view and recover such files and folders. In addition, file attributes and MFT records can be saved (including alternate NTFS data streams).
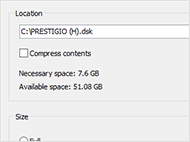
Working with drive images
The program lets you create an image of a logical partition or a whole physical drive. This enables you to work with a copy of data on a carrier to minimize the risk of loosing data due to inappropriate user actions.
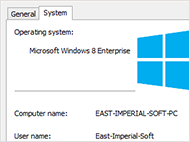
Made for Microsoft Windows
Magic Office Recovery features familiar usage experience and mimics look and feel of Windows Explorer. It runs in Microsoft Windows XP, Vista, Windows 8, 10 and 2008 Server. 32-bit and 64-bit editions are supported.